Image Credit: Pixabay
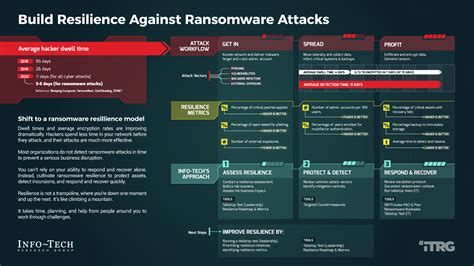
Imagine this – every 39 seconds, a devastating ransomware attack strikes. That’s over 2200 organizations facing cyber extortion daily. These attacks are like evolving predators, constantly changing their tactics to outsmart even the most vigilant cybersecurity measures.
The Sophistication of Ransomware Attacks
From slow encryption to shadow techniques and byte replacement, hackers leave no stone unturned in their mission to compromise valuable data. Moreover, they’re now resorting to threatening data leaks unless hefty ransoms are paid promptly.
No industry is safe from these malicious assaults; supply chains, healthcare facilities, and local governments have all fallen prey to these insidious attacks. Scott Cooper, VP of Field Engineering at Index Engines aptly notes the severity of the situation.
The Costly Gamble of Paying Ransoms
While many organizations see paying the ransom as a quick fix solution, reality paints a different picture. Studies reveal that recovering from such attacks costs organizations ten times more than the actual ransom demand itself.
An alarming statistic further highlights that nearly all ransomware attacks involve attempts to infiltrate backups, with an unfortunate success rate of 57%. The aftermath extends beyond financial burdens; it causes operational chaos leading to significant downtime and productivity losses.
Impact on Business Continuity
The repercussions extend far beyond monetary losses; operational disruptions can lead to long-term damage affecting business sustainability. Additionally, failure in safeguarding sensitive information can result in severe penalties under regulations like GDPR and HIPAA.
Breaking the Cycle
Paying ransoms only fuels cybercrime by providing funds for attackers’ next wave of assaults. Instead of succumbing to extortion demands, organizations must adopt proactive recovery strategies that ensure data integrity through secure backups and robust detection mechanisms.
By prioritizing recovery over payment, companies not only thwart ongoing attacks but also contribute significantly towards halting the vicious cycle of funding future cyber threats.
Post-Attack Recovery Measures
Despite heavy investments in security measures post-attack recovery plans often fall short due to persistent vulnerabilities. Organizations must enhance their defenses by implementing comprehensive data integrity strategies and forensic analysis for improved threat detection.
To stay ahead in this cyber warfare battleground, businesses need unified approaches that guarantee swift restoration while minimizing disruption effectively during recovery processes.
The Road Ahead: Building Resilience
Preparation is key! Strengthened defenses require collective efforts encompassing multi-factor authentication setups, network segregation protocols,and vigilantly monitored intrusion detection systems. Regular audits help identify weak spots before attackers exploit them.
A proactive stance through incident response training equips teams with necessary skills for coordinated defensive actions against potential threats.At its core lies a comprehensive recovery plan regularly reviewed,tested,and updated ensuring minimal downtime during crisis situations.
In conclusion,besides prevention,a focus on robust,reliable recovery strategies plays a fundamental role in fortifying organizational cybersecurity resilience.By fostering a culture that emphasizes data integrity,cybercriminals can be deterred effectively,paving the way for a safer digital landscape.





Leave feedback about this